What are 'Unknown Unknowns'?
When critical vulnerabilities in Internet-facing assets are not yet publicly disclosed, they can provide unfettered access to organizations’ networks. Threat actors’ exploitation of these vulnerabilities are prime examples of “unknown unknowns” – behaviors which security teams are not even aware that they are not aware of.
Therefore, it is not surprising that zero-day vulnerabilities in Internet-facing assets are so attractive to state-linked actors and cybercriminals. These criminals will abuse the access these vulnerabilities afford them to progress towards harmful or disruptive objectives. This trend in threat actor activity was particularly salient in January 2024, following the disclosure of two critical vulnerabilities in Ivanti Connect Secure (CS) and Ivanti Policy Secure (PS) appliances. The widespread exploitation of these vulnerabilities was mirrored across Darktrace’s customer base in mid-January 2024, with Darktrace’s Security Operations Center (SOC) and Threat Research teams observing a surge in malicious activities targeting customers’ CS/PS appliances.
Vulnerabilities in Ivanti CS/PS
On January 10, 2024, Ivanti published a Security Advisory [1] and a Knowledge Base article [2] relating to the following two vulnerabilities in Ivanti Connect Secure (CS) and Ivanti Policy Secure (PS):
- CVE-2023-46805 (CVSS: 8.2; Type: Authentication bypass vulnerability)
- CVE-2024-21887 (CVSS: 9.1; Type: Command injection vulnerability)
Conjoined exploitation of these vulnerabilities allows for unauthenticated, remote code execution (RCE) on vulnerable Ivanti systems. Volexity [3] and Mandiant [4] reported clusters of CS/PS compromises, tracked as UTA0178 and UNC5221 respectively. UTA0178 and UNC5221 compromises involve exploitation of CVE-2023-46805 and CVE-2024-21887 to deliver web shells and JavaScript credential harvesters to targeted CS/PS appliances. Both Volexity and Mandiant linked these compromises to a likely espionage-motivated, state-linked actor. GreyNoise [5] and Volexity [6] also reported likely cybercriminal activities targeting CS/PS appliances to deliver cryptominers.
The scale of this recent Ivanti CS/PS exploitation is illustrated by research findings recently shared by Censys [7]. According to these findings, as of January 22, around 1.5% of 26,000 Internet-exposed Ivanti CS appliances have been compromised, with the majority of compromised hosts falling within the United States. As cybercriminal interest in these Ivanti CS/PS vulnerabilities continues to grow, it is likely that so too will the number of attacks targeting them.
Observed Malicious Activities
Since January 15, 2024, Darktrace’s SOC and Threat Research team have observed a significant volume of malicious activities targeting customers’ Ivanti CS/PS appliances. Amongst the string of activities that were observed, the following threads were identified as salient:
- Exploit validation activity
- Exfiltration of system information
- Delivery of C2 implant from AWS
- Delivery of JavaScript credential stealer
- SimpleHelp usage
- Encrypted C2 on port 53
- Delivery of cryptominer
Exploit Validation Activity
Malicious actors were observed using the out-of-band application security testing (OAST) services, Interactsh and Burp Collaborator, to validate exploits for CS/PS vulnerabilities. Malicious use of OAST services for exploit validation is common and has been seen in the early stages of previous campaigns targeting Ivanti systems [8]. In this case, the Interact[.]sh exploit tests were evidenced by CS/PS appliances making GET requests with a cURL User-Agent header to subdomains of 'oast[.]live', 'oast[.]site', 'oast[.]fun', 'oast[.]me', 'oast[.]online' and 'oast[.]pro'. Burp Collaborator exploit tests were evidenced by CS/PS appliances making GET requests with a cURL User-Agent header to subdomains of ‘collab.urmcyber[.]xyz’ and ‘dnslog[.]store’.




Exfiltration of System Information
The majority of compromised CS/PS appliances identified by Darktrace were seen using cURL to transfer hundreds of MBs of data to the external endpoint, 139.180.194[.]132. This activity appeared to be related to a threat actor attempting to exfiltrate system-related information from CS/PS appliances. These data transfers were carried out via HTTP on ports 443 and 80, with the Target URIs ‘/hello’ and ‘/helloq’ being seen in the relevant HTTP POST requests. The files sent over these data transfers were ‘.dat’ and ‘.sys’ files with what seems to be the public IP address of the targeted appliance appearing in each file’s name.


Delivery of Command-and-Control (C2) implant from Amazon Web Services (AWS)
In many of the compromises observed by Darktrace, the malicious actor in question was observed delivering likely Rust-based ELF payloads to the CS/PS appliance from the AWS endpoints, archivevalley-media.s3.amazonaws[.]com, abode-dashboard-media.s3.ap-south-1.amazonaws[.]com, shapefiles.fews.net.s3.amazonaws[.]com, and blooming.s3.amazonaws[.]com. In one particular case, these downloads were immediately followed by the delivery of an 18 MB payload (likely a C2 implant) from the AWS endpoint, be-at-home.s3.ap-northeast-2.amazonaws[.]com, to the CS/PS appliance. Post-delivery, the implant seems to have initiated SSL beaconing connections to the external host, music.farstream[.]org. Around this time, Darktrace also observed the actor initiating port scanning and SMB enumeration activities from the CS/PS appliance, likely in preparation for moving laterally through the network.

Delivery of JavaScript credential stealer
In a small number of observed cases, Darktrace observed malicious actors delivering what appeared to be a JavaScript credential harvester to targeted CS/PS appliances. The relevant JavaScript code contains instructions to send login credentials to likely compromised websites. In one case, the website, www.miltonhouse[.]nl, appeared in the code snippet, and in another, the website, cpanel.netbar[.]org, was observed. Following the delivery of this JavaScript code, HTTPS connections were observed to these websites. This likely credential harvester appears to strongly resemble the credential stealer observed by Mandiant (dubbed ‘WARPWIRE’) in UNC5221 compromises and the credential stealer observed by Veloxity in UTA0178 compromises.





The usage of this JavaScript credential harvester did not occur in isolation, but rather appears to have occurred as part of a chain of activity involving several further steps. The delivery of the ‘www.miltonhouse[.]nl’ JavaScript stealer seems to have occurred as a step in the following attack chain:
1. Ivanti CS/PS appliance downloads a 8.38 MB ELF file over HTTP (with Target URI ‘/revsocks_linux_amd64’) from 188.116.20[.]38
2. Ivanti CS/PS appliance makes a long SSL connection (JA3 client fingerprint: 19e29534fd49dd27d09234e639c4057e) over port 8444 to 185.243.112[.]245, with several MBs of data being exchanged
3. Ivanti CS/PS appliance downloads a Perl script over HTTP (with Target URI ‘/login.txt’) from 188.116.20[.]38
4. Ivanti CS/PS appliance downloads a 1.53 ELF MB file over HTTP (with Target URI ‘/aparche2’) from 91.92.240[.]113
5. Ivanti CS/PS appliance downloads a 4.5 MB ELF file over HTTP (with Target URI ‘/agent’) from 91.92.240[.]113
6. Ivanti CS/PS appliance makes a long SSL connection (JA3 client fingerprint: 19e29534fd49dd27d09234e639c4057e) over port 11601 to 45.9.149[.]215, with several MBs of data being exchanged
7. Ivanti CS/PS appliance downloads Javascript credential harvester over HTTP (with Target URI ‘/auth.js’) from 91.92.240[.]113
8. Ivanti CS/PS appliance downloads a Perl script over HTTP (with Target URI ‘/login.cgi’) from 91.92.240[.]113
9. Ivanti CS/PS appliance makes a long SSL connection (JA3 client fingerprint: 19e29534fd49dd27d09234e639c4057e) over port 11601 to 91.92.240[.]71, with several MBs of data being exchanged
10. Ivanti CS/PS appliance makes a long SSL connection (JA3 client fingerprint: 19e29534fd49dd27d09234e639c4057e) over port 11601 to 45.9.149[.]215, with several MBs of data being exchanged
11. Ivanti CS/PS appliance makes a long SSL connection (JA3 client fingerprint: 19e29534fd49dd27d09234e639c4057e) over port 8080 to 91.92.240[.]113, with several MBs of data being exchanged
12. Ivanti CS/PS appliance makes a long SSL connection (JA3 client fingerprint: 19e29534fd49dd27d09234e639c4057e) over port 11601 to 45.9.149[.]112, with several MBs of data being exchanged
These long SSL connections likely represent a malicious actor creating reverse shells from the targeted CS/PS appliance to their C2 infrastructure. Whilst it is not certain that these behaviors are part of the same attack chain, the similarities between them (such as the Target URIs, the JA3 client fingerprint and the use of port 11601) seem to suggest a link.




SimpleHelp Usage
After gaining a foothold on vulnerable CS/PS appliances, certain actors attempted to deepen their foothold within targeted networks. In several cases, actors were seen using valid account credentials to pivot over RDP from the vulnerable CS/PS appliance to other internal systems. Over these RDP connections, the actors appear to have installed the remote support tool, SimpleHelp, onto targeted internal systems, as evidenced by these systems’ subsequent HTTP requests. In one of the observed cases, a lateral movement target downloaded a 7.33 MB executable file over HTTP (Target URI: /ta.dat; User-Agent header: Microsoft BITS/7.8) from 45.9.149[.]215 just before showing signs of SimpleHelp usage. The apparent involvement of 45.9.149[.]215 in these SimpleHelp threads may indicate a connection between them and the credential harvesting thread outlined above.


Encrypted C2 over port 53
In a handful of the recently observed CS/PS compromises, Darktrace identified malicious actors dropping a 16 MB payload which appears to use SSL-based C2 communication on port 53. C2 communication on port 53 is a commonly used attack method, with various malicious payloads, including Cobalt Strike DNS, being known to tunnel C2 communications via DNS requests on port 53. Encrypted C2 communication on port 53, however, is less common. In the cases observed by Darktrace, payloads were downloaded from 103.13.28[.]40 and subsequently reached back out to 103.13.28[.]40 over SSL on port 53.


Delivery of cryptominer
As is often the case, financially motivated actors also appeared to have sought to exploit the Ivanti appliances, with actors observed exploiting CS/PS appliances to deliver cryptomining malware. In one case, Darktrace observed an actor installing a Monero cryptominer onto a vulnerable CS/PS appliance, with the miner being downloaded via HTTP on port 8089 from 192.252.183[.]116.



Potential Pre-Ransomware Post-Compromise Activity
In one observed case, a compromise of a customer’s CS appliance was followed by an attacker using valid account credentials to connect to the customer’s CS VPN subnet. The attacker used these credentials to pivot to other parts of the customer’s network, with tools and services such as PsExec, Windows Management Instrumentation (WMI) service, and Service Control being abused to facilitate the lateral movement. Other Remote Monitoring and Management (RMM) tools, such as AnyDesk and ConnectWise Control (previously known as ScreenConnect), along with certain reconnaissance tools such as Netscan, Nmap, and PDQ, also appear to have been used. The attacker subsequently exfiltrated data (likely via Rclone) to the file storage service, put[.]io, potentially in preparation for a double extortion ransomware attack. However, at the time of writing, it was not clear what the relation was between this activity and the CS compromise which preceded it.
Darktrace Coverage
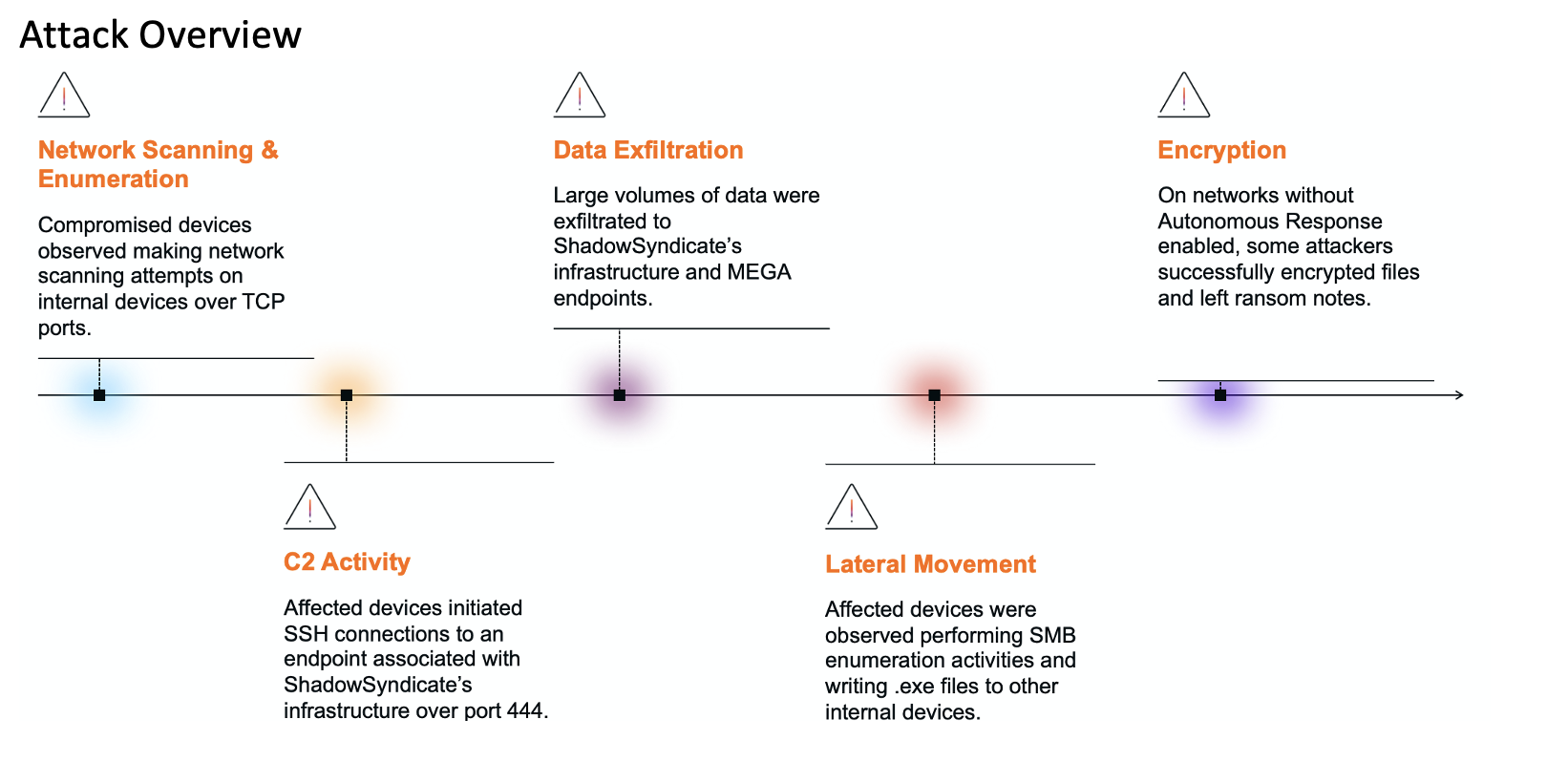
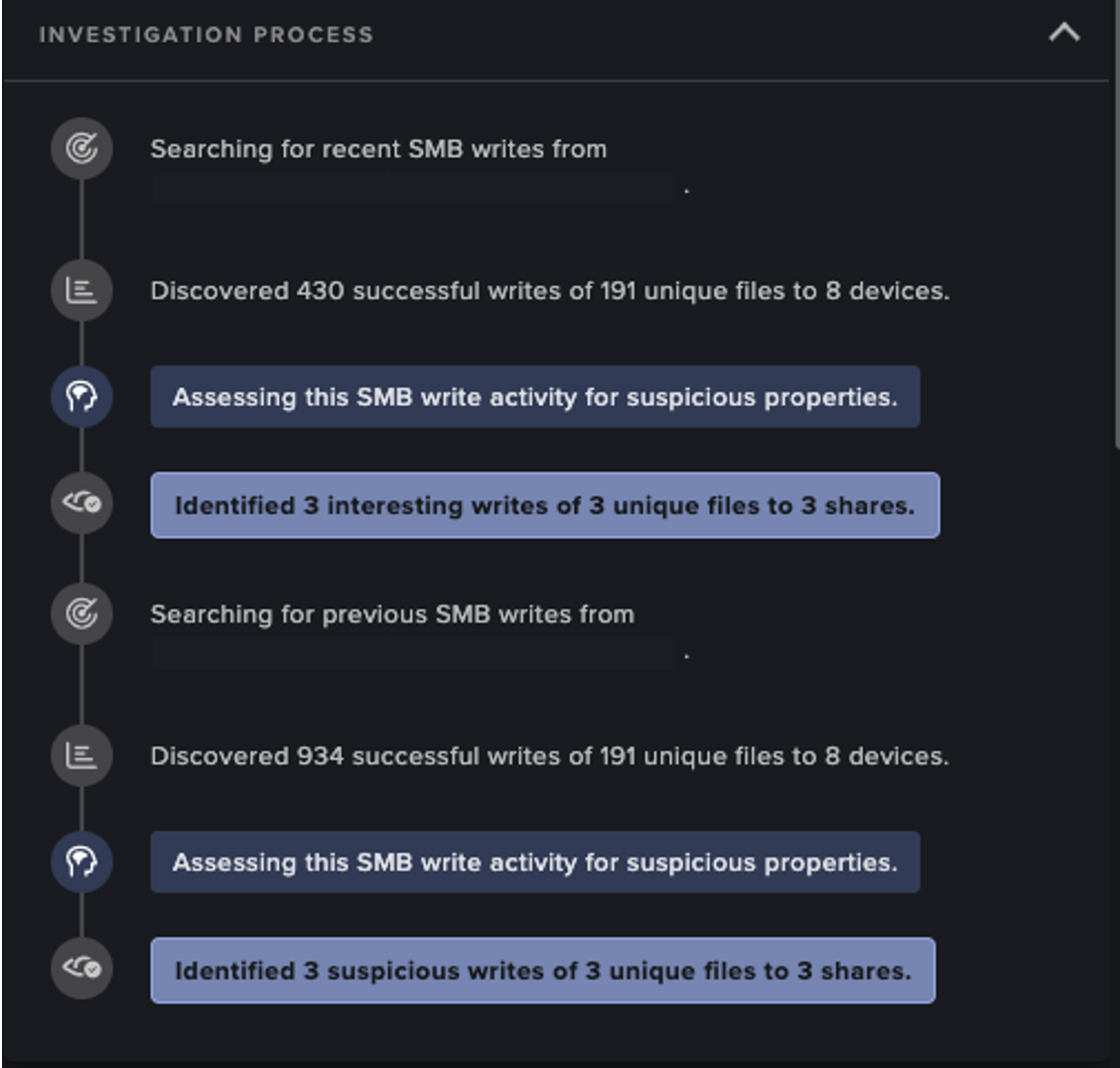
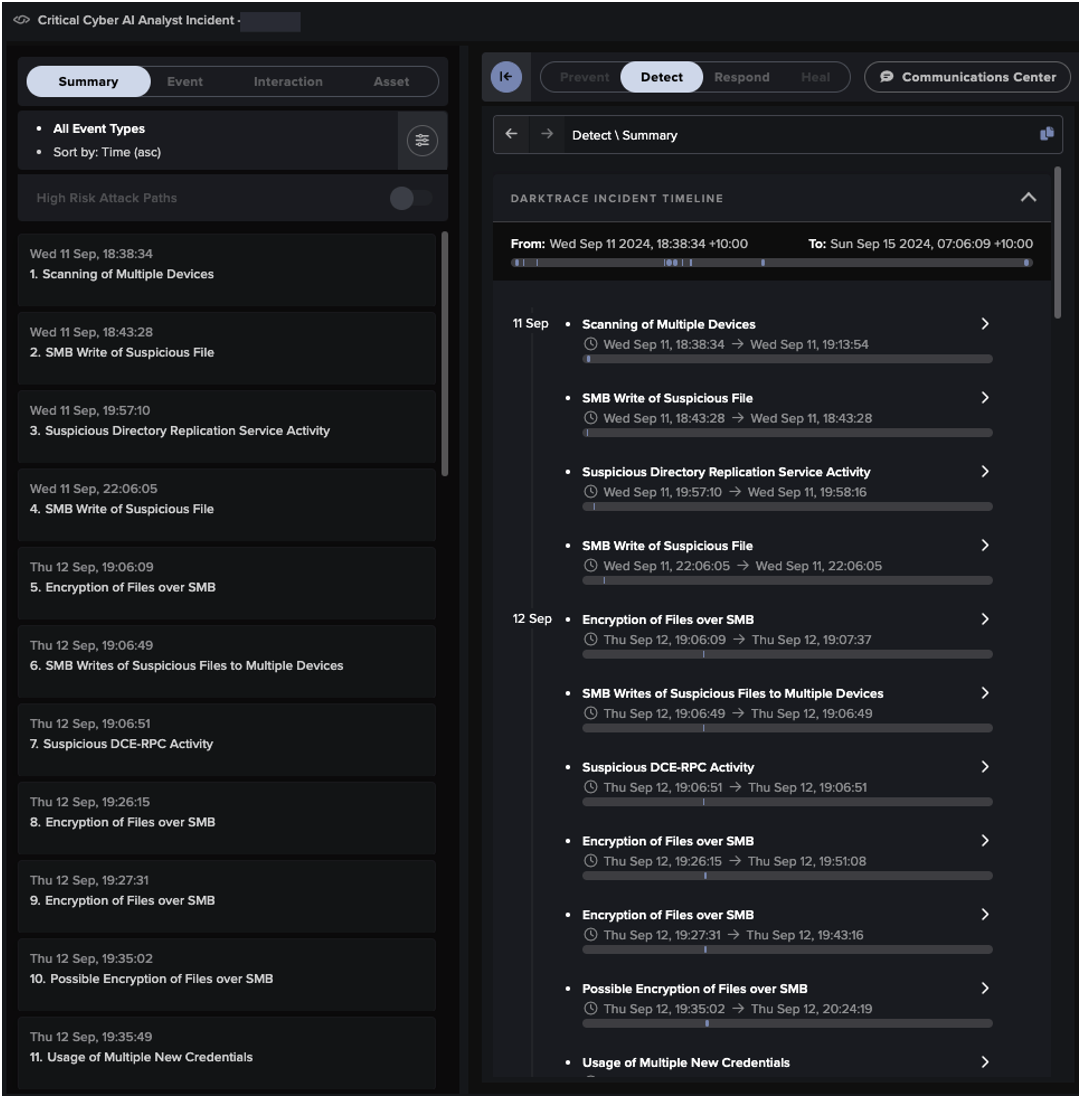
Darktrace has observed malicious actors carrying out a variety of post-exploitation activities on Internet-exposed CS/PS appliances, ranging from data exfiltration to the delivery of C2 implants and crypto-miners. These activities inevitably resulted in CS/PS appliances displaying patterns of network traffic greatly deviating from their typical “patterns of life”.
Darktraceidentified these deviations and generated a variety of model breaches (i.e, alerts) highlighting the suspicious activity. Darktrace’s Cyber AI Analyst™ autonomously investigated the ongoing compromises and connected the individual model breaches, viewing them as related incidents rather than isolated events. When active and configured in autonomous response mode, Darktracntainted attackers’ operations by autonomously blocking suspicious patterns of network traffic as soon as they were identified by Darktrace
The exploit validation activities carried out by malicious actors resulted in CS/PS servers making HTTP connections with cURL User-Agent headers to endpoints associated with OAST services such as Interactsh and Burp Collaborator. Darktrace recognized that this HTTP activity was suspicious for affected devices, causing the following models to breach:
- Compromise / Possible Tunnelling to Bin Services
- Device / Suspicious Domain
- Anomalous Server Activity / New User Agent from Internet Facing System
- Device / New User Agent


Malicious actors’ uploads of system information to 139.180.194[.]132 resulted in cURL POST requests being sent from the targeted CS/PS appliances. Darktrace DETECT judged these HTTP POST requests to be anomalous, resulting in combinations of the following model breaches:
- Anomalous Connection / Posting HTTP to IP Without Hostname
- Anomalous Server Activity / Outgoing from Server
- Anomalous Server Activity / New User Agent from Internet Facing System
- Unusual Activity / Unusual External Data Transfer
- Unusual Activity / Unusual External Data to New Endpoint
- Anomalous Connection / Data Sent to Rare Domain


The installation of AWS-hosted C2 implants onto vulnerable CS/PS appliances resulted in beaconing connections which Darktrace recognized as anomalous, leading to the following model breaches:
- Compromise / Beacon to Young Endpoint
- Compromise / Beaconing Activity To External Rare
- Compromise / High Volume of Connections with Beacon Score
When enabled in autonomous response mode, Darktrace's Autonomous Response was able to follow up these detections by blocking affected devices from connecting externally over port 80, 443, 445 or 8081, effectively shutting down the attacker’s beaconing activity.

The use of encrypted C2 on port 53 by malicious actors resulted in CS/PS appliances making SSL connections over port 53. Darktrace judged this port to be uncommon for SSL traffic and consequently generated the following model breach:
- Anomalous Connection / Application Protocol on Uncommon Port



Malicious actors’ attempts to run cryptominers on vulnerable CS/PS appliances resulted in downloads of Bash scripts and JSON files from external endpoints rarely visited by the CS/PS appliances themselves or by neighboring systems. Darktrace identified these deviations in device behavior and generated the following model breaches:
- Anomalous File / Script from Rare External Location
- Anomalous File / Internet Facing System File Download
Darktrace's Autonomous Response, when configured to respond autonomously, was subsequently able to carry out a number of actions to contain the attacker’s activity. This included blocking all outgoing traffic on offending devices and enforcing a “pattern of life” on devices ensuring they had to adhere to expected network behavior.


The use of RDP to move laterally and spread SimpleHelp to other systems resulted in CS/PS appliances using privileged credentials to initiate RDP sessions. These RDP sessions, and the subsequent traffic resulting from usage of SimpleHelp, were recognized by Darktrace as being highly out of character, prompting the following model breaches:
- Anomalous Connection / Unusual Admin RDP Session
- Device / New User Agent
- Anomalous Connection / New User Agent to IP Without Hostname
- Compromise / Suspicious HTTP Beacons to Dotted Quad
- Anomalous File / Anomalous Octet Stream (No User Agent)
- Anomalous Server Activity / Rare External from Server



Conclusion
The recent widespread exploitation of Ivanti CS/PS is a stark reminder of the threat posed by malicious actors armed with exploits for Internet-facing assets.
Based on the telemetry available to Darktrace, a wide range of malicious activities were carried out against CS/PS appliances, likely via exploitation of the recently disclosed CVE-2023-46805 and CVE-2024-21887 vulnerabilities.
These activities include the usage of OAST services for exploit validation, the exfiltration of system information to 139.180.194[.]132, the delivery of AWS-hosted C2 implants, the delivery of JavaScript credential stealers, the usage of SimpleHelp, the usage of SSL-based C2 on port 53, and the delivery of crypto-miners. These activities are far from exhaustive, and many more activities will undoubtedly be uncovered as the situation develops and our understanding grows.
While there were no patches available at the time of writing, Ivanti stated that they were expected to be released shortly, with the “first version targeted to be available to customers the week of 22 January 2023 and the final version targeted to be available the week of 19 February” [9].
Fortunately for vulnerable customers, in their absence of patches Darktrace was able to identify and alert for anomalous network activity that was carried out by malicious actors who had been able to successfully exploit the Ivanti CS and PS vulnerabilities. While the activity that followed these zero-day vulnerabilities may been able to have bypass traditional security tools reliant upon existing threat intelligence and indicators of compromise (IoCs), Darktrace’s anomaly-based approach allows it to identify such activity based on the subtle deviations in a devices behavior that typically emerge as threat actors begin to work towards their goals post-compromise.
In addition to Darktrace’s ability to identify this type of suspicious behavior, its autonomous response technology, Darktrace's Autonomous Response is able to provide immediate follow-up with targeted mitigative actions to shut down malicious activity on affected customer environments as soon as it is detected.
Credit to: Nahisha Nobregas, SOC Analyst, Emma Foulger, Principle Cyber Analyst, and the Darktrace Threat Research Team
Appendices
List of IoCs Possible IoCs:
- curl/7.19.7 (i686-redhat-linux-gnu) libcurl/7.63.0 OpenSSL/1.0.2n zlib/1.2.3
- curl/7.19.7 (i686-redhat-linux-gnu) libcurl/7.63.0 OpenSSL/1.0.2n zlib/1.2.7
Mid-high confidence IoCs:
- http://139.180.194[.]132:443/hello
- http://139.180.194[.]132:443/helloq
- http://blooming.s3.amazonaws[.]com/Ea7fbW98CyM5O (SHA256 hash: 816754f6eaf72d2e9c69fe09dcbe50576f7a052a1a450c2a19f01f57a6e13c17)
- http://abode-dashboard-media.s3.ap-south-1.amazonaws[.]com/kaffMm40RNtkg (SHA256 hash: 47ff0ae9220a09bfad2a2fb1e2fa2c8ffe5e9cb0466646e2a940ac2e0cf55d04)
- http://archivevalley-media.s3.amazonaws[.]com/bbU5Yn3yayTtV (SHA256 hash: c7ddd58dcb7d9e752157302d516de5492a70be30099c2f806cb15db49d466026)
- http://shapefiles.fews.net.s3.amazonaws[.]com/g6cYGAxHt4JC1 (SHA256 hash: c26da19e17423ce4cb4c8c47ebc61d009e77fc1ac4e87ce548cf25b8e4f4dc28)
- http://be-at-home.s3.ap-northeast-2.amazonaws[.]com/2ekjMjslSG9uI
- music.farstream[.]org • 104.21.86[.]153 / 172.67.221[.]78
- http://197.243.22[.]27/3.js
- http://91.92.240[.]113/auth.js
- www.miltonhouse[.]nl • 88.240.53[.]22
- cpanel.netbar[.]org • 146.19.212[.]12
- http://188.116.20[.]38/revsocks_linux_amd64
- 185.243.112[.]245:8444
- http://188.116.20[.]38/login.txt
- http://91.92.240[.]113/aparche2 (SHA256 hash: 9d11c3cf10b20ff5b3e541147f9a965a4e66ed863803c54d93ba8a07c4aa7e50)
- http://91.92.240[.]113/agent (SHA256 hash: 7967def86776f36ab6a663850120c5c70f397dd3834f11ba7a077205d37b117f)
- 45.9.149[.]215:11601
- 45.9.149[.]112:11601
- http://91.92.240[.]113/login.cgi
- 91.92.240[.]71:11601
- 91.92.240[.]113:8080
- http://45.9.149[.]215/ta.dat (SHA256 hash: 4bcf1333b3ad1252d067014c606fb3a5b6f675f85c59b69ca45669d45468e923)
- 91.92.241[.]18
- 94.156.64[.]252
- http://144.172.76[.]76/lin86
- 144.172.122[.]14:443
- http://185.243.115[.]58:37586/
- http://103.13.28[.]40/linb64.png
- 103.13.28[.]40:53
- 159.89.82[.]235:8081
- http://192.252.183[.]116:8089/u/123/100123/202401/d9a10f4568b649acae7bc2fe51fb5a98.sh
- http://192.252.183[.]116:8089/u/123/100123/202401/sshd
- http://192.252.183[.]116:8089/u/123/100123/202401/31a5f4ceae1e45e1a3cd30f5d7604d89.json
- http://103.27.110[.]83/module/client_amd64
- http://103.27.110[.]83/js/bootstrap.min.js?UUID=...
- http://103.27.110[.]83/js/jquery.min.js
- http://95.179.238[.]3/bak
- http://91.92.244[.]59:8080/mbPHenSdr6Cf79XDAcKEVA
- 31.220.30[.]244
- http://172.245.60[.]61:8443/SMUkbpX-0qNtLGsuCIuffAOLk9ZEBCG7bIcB2JT6GA/
- http://172.245.60[.]61/ivanti
- http://89.23.107[.]155:8080/l-5CzlHWjkp23gZiVLzvUg
- http://185.156.72[.]51:8080/h7JpYIZZ1-rrk98v3YEy6w
- http://185.156.72[.]51:8080/8uSQsOTwFyEAsXVwbAJ2mA
- http://185.156.72[.]51:8080/vuln
- 185.156.72[.]51:4440
- 185.156.72[.]51:8080
- 185.156.72[.]51:4433
- 185.156.72[.]51:4446
- 185.156.72[.]51:4445
- http://185.156.72[.]51/set.py
- 185.156.72[.]51:7777
- 45.9.151[.]107:7070
- 185.195.59[.]74:7070
- 185.195.59[.]74:20958
- 185.195.59[.]74:34436
- 185.195.59[.]74:37464
- 185.195.59[.]74:41468
References
[4] https://www.mandiant.com/resources/blog/suspected-apt-targets-ivanti-zero-day
[5] https://www.greynoise.io/blog/ivanti-connect-secure-exploited-to-install-cryptominers
[6] https://www.volexity.com/blog/2024/01/18/ivanti-connect-secure-vpn-exploitation-new-observations/
[7] https://censys.com/the-mass-exploitation-of-ivanti-connect-secure/