Understanding the Network Security Market
Old tools blind to new threats
With the rise of GenAI and novel attacks, organizations can no longer rely solely on traditional network security solutions that depend on historical attack data, such as signatures and detection rules, to identify threats. However, in many cases network security vendors and traditional solutions like IDS/IPS focus on detecting known attacks using historical data. What happens is organizations are left vulnerable to unknown and novel threats, as these approaches only detect known malicious behavior and cannot keep up with unknown threats or zero-day attacks.
Advanced threats
Darktrace's End of Year Threat Report for 2023 highlights significant changes in the cyber threat landscape, particularly due to advancements in technology such as generative AI. The report notes a substantial increase in sophisticated attacks, including those utilizing generative AI, which have made it more challenging for traditional security measures to keep up. The report also details the rise of multi-functional malware, like Black Basta ransomware, which not only encrypts data for ransom but also spreads other types of malware such as the Qbot banking trojan. These complex attacks are increasingly being deployed by advanced cybercriminal groups, underscoring the need for organizations to adopt advanced security measures that can detect and respond to novel threats in real-time.
Defenders need a solution that can level the playing field, especially when they are operating with limited resources and getting overloaded with endless alerts. Most network security tools on the market have a siloed approach and do not integrate with the rest of an organization’s digital estate, but attackers don’t operate in a single domain.
Disparate workforce
With so many organizations continuing to support a remote or hybrid working environment, the need to secure devices that are outside the corporate network or off-VPN is increasingly important. While endpoint protection or endpoint detection and response (EDR) tools are a fundamental part of any security stack, it’s not possible to install an agent on every device, which can leave blind spots in an organization’s attack surface. Managing trust and access policies is also necessary to protect identities, however this comes with its own set of challenges in terms of implementation and minimizing business disruption.
This blog will dive into these challenges and show examples of how Darktrace has helped mitigate risk and stop novel and never-before-seen threats.
Network Security Challenge 1: Managing trust
What is trust in cybersecurity?
Trust in cybersecurity means that an entity can be relied upon. This can involve a person, organization, or system to be authorized or authenticated by proving their identity is legitimate and can be trusted to have access to the network or sensitive information.
Why is trust important in cybersecurity?
Granting access and privileges to your workforce and select affiliates has profound implications for cybersecurity, brand reputation, regulatory compliance, and financial liability. In a traditional network security model, traffic gets divided into two categories — trusted and untrusted — with some entities and segments of the network deemed more creditable than others.
How do you manage trust in cybersecurity?
Zero trust is too little, but any is too much.
Modern network security challenges point to an urgent need for organizations to review and update their approaches to managing trust. External pressure to adopt zero trust security postures literally suggests trusting no one, but that impedes your freedom
to do business. IT leaders need a proven but practical process for deciding who should be allowed to use your network and how.
Questions to ask in updating Trusted User policies include:
- What process should you follow to place trust in third
parties and applications? - Do you subject trusted entities to testing and other due
diligence first? - How often do you review this process — and trusted
relationships themselves — after making initial decisions? - How do you tell when trusted users should no longer be
trusted?
Once trust has been established, security teams need new and better ways to autonomously verify that those transacting within your network are indeed those trusted users that they claim to be, taking only the authorized actions you’ve allowed them to take.
Exploiting trust in the network
Insider threats have a major head start. The opposite of attacks launched by nameless, faceless strangers, insider threats originate through parties once deemed trustworthy. That might mean a current or former member of your workforce or a partner, vendor, investor, or service provider authorized by IT to access corporate systems and data. Threats also arise when a “pawn” gets unwittingly tricked into disclosing credentials or downloading malware.
Common motives for insider attacks include revenge, stealing or leaking sensitive data, taking down IT systems, stealing assets or IP, compromising your organization’s credibility, and simply harassing your workforce. Put simply, rules and signatures based security solutions won’t flag insider threats because an insider does not immediately present themselves as an intruder. Insider threats can only be stopped by an evolving understanding of ‘normal’ for every user that immediately alerts your team when trusted users do something strange.
“By 2026, 10% of large enterprises will have a comprehensive, mature and measurable zero-trust program in place, up from less than 1% today.” [1]
Use Case: Darktrace spots an insider threat
Darktrace / OT detected a subtle deviation from normal behavior when a reprogram command was sent by an engineering workstation to a PLC controlling a pump, an action an insider threat with legitimized access to OT systems would take to alter the physical process without any malware involved. In this instance, AI Analyst, Darktrace’s investigation tool that triages events to reveal the full security incident, detected the event as unusual based on multiple metrics including the source of the command, the destination device, the time of the activity, and the command itself.
As a result, AI Analyst created a complete security incident, with a natural language summary, the technical details of the activity, and an investigation process explaining how it came to its conclusion. By leveraging Explainable AI, a security team can quickly triage and escalate Darktrace incidents in real time before it becomes disruptive, and even when performed by a trusted insider.
Read more about insider threats here
Network Security Challenge 2: Stopping Ransomware at every stage
What is Ransomware?
Ransomware is a type of malware that encrypts valuable files on a victim’s device, denying the account holder access, and demanding money in exchange for the encryption key. Ransomware has been increasingly difficult to deal with, especially with ransom payments being made in crypto currency which is untraceable. Ransomware can enter a system by clicking a link dangerous or downloading malicious files.
Avoiding ransomware attacks ranks at the top of most CISOs’ and risk managers’ priority lists, and with good reason. Extortion was involved in 25% of all breaches in 2022, with front-page attacks wreaking havoc across healthcare, gas pipelines, food processing plants, and other global supply chains. [2]
What else is new?
The availability of “DIY” toolkits and subscription-based ransom- ware-as-a-service (RaaS) on the dark web equips novice threat actors to launch highly sophisticated attacks at machine speed. For less than $500, virtually anyone can acquire and tweak RaaS offerings such as Philadelphia that come with accessible customer interfaces, reviews, discounts, and feature updates — all the signature features of commercial SaaS offerings.
Darktrace Cyber AI breaks the ransomware cycle
The preeminence of ransomware keeps security teams on high alert for indicators of attack but hypervigilance — and too many tools churning out too many alerts — quickly exhausts analysts’ bandwidth. To reverse this trend, AI needs to help prioritize and resolve versus merely detect risk.
Darktrace uses AI to recognize and contextualize possible signs of ransomware attacks as they appear in your network and across multiple domains. Viewing behaviors in the context of your organization’s normal ‘pattern of life’ updates and enhances detection that watches for a repeat of previous techniques.
Darktrace's AI brings the added advantage of continuously analyzing behavior in your environment at machine speed.
Darktrace AI also performs Autonomous Response, shutting down attacks at every stage of the ransomware cycle, including the first telltale signs of exfiltration and encryption of data for extortion purposes.
Use Case: Stopping Hive Ransomware attack
Hive is distributed via a RaaS model where its developers update and maintain the code, in return for a percentage of the eventual ransom payment, while users (or affiliates) are given the tools to carry out attacks using a highly sophisticated and complex malware they would otherwise be unable to use.
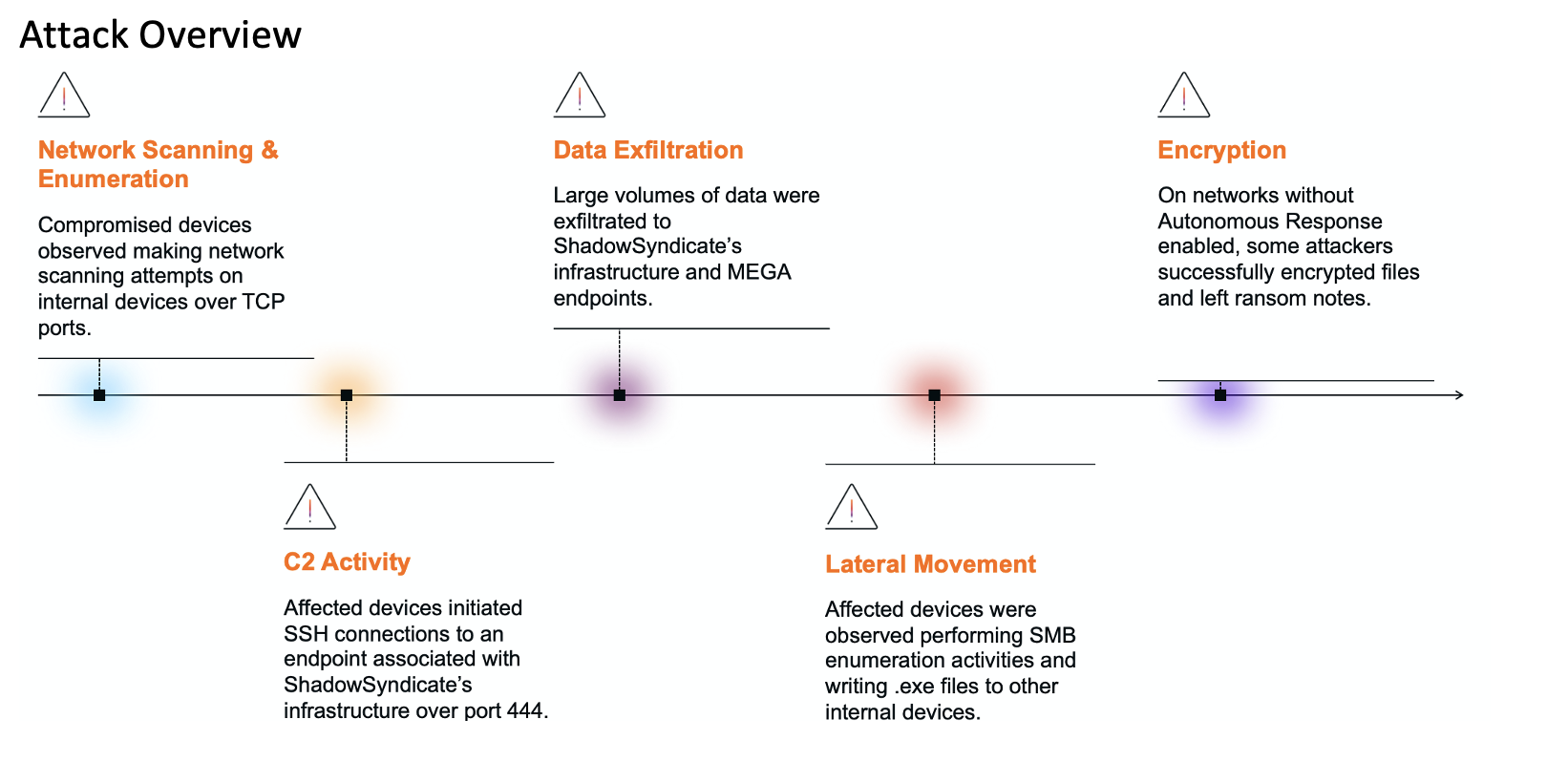
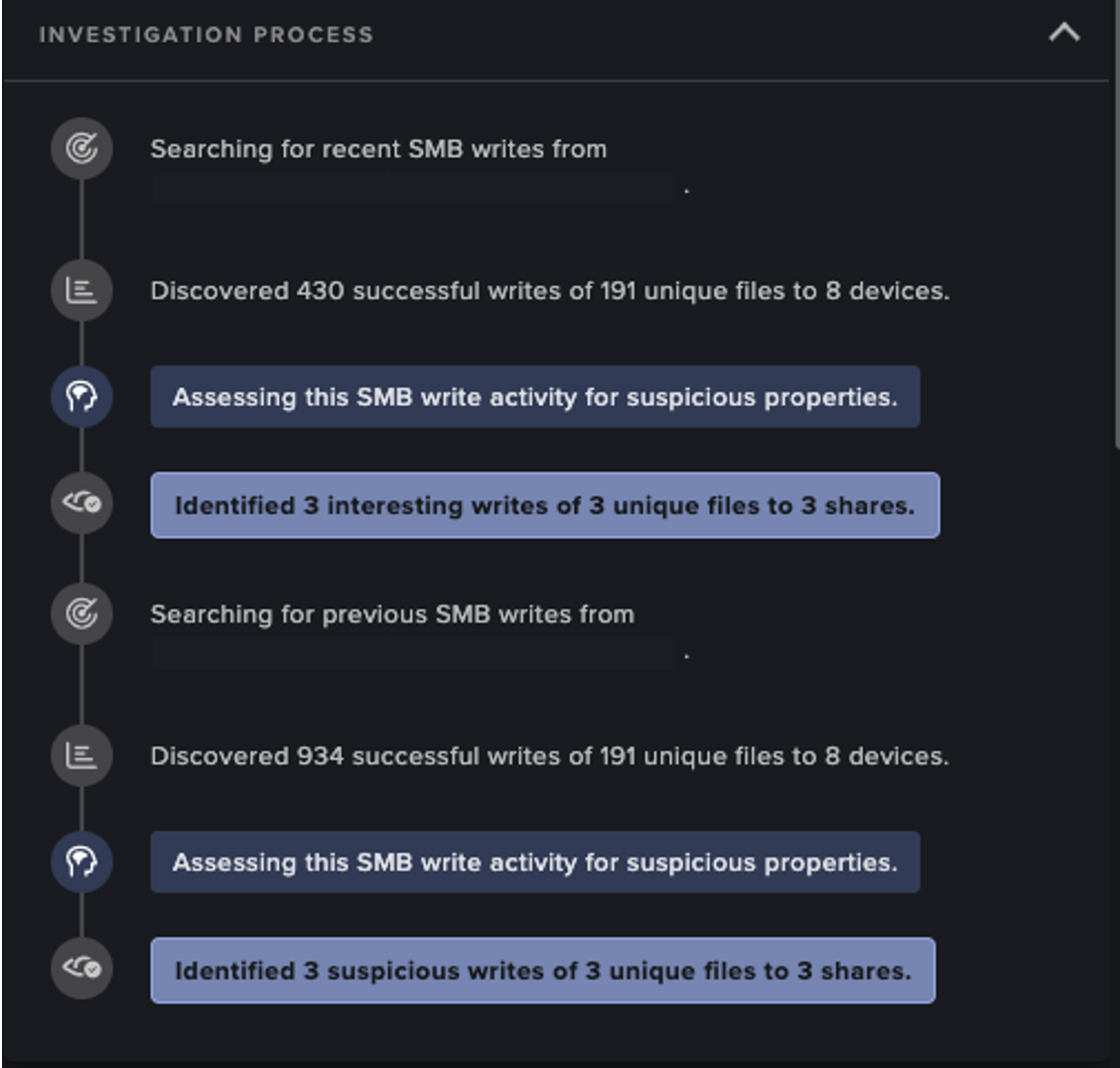
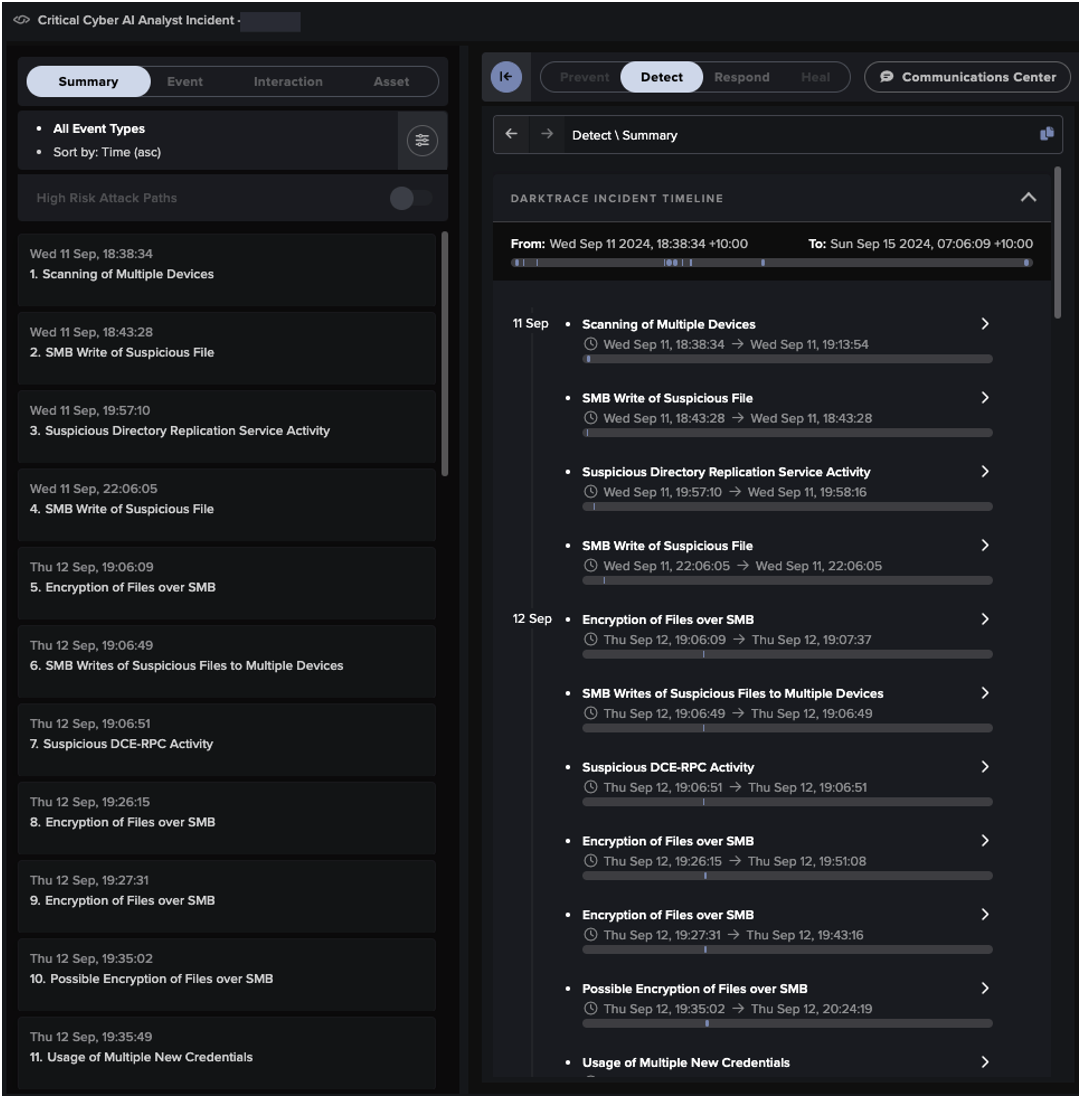
In early 2022, Darktrace / NETWORK identified several instances of Hive ransomware on the networks of multiple customers. Using its anomaly-based detection, Darktrace was able to successfully detect the attacks and multiple stages of the kill chain, including command and control (C2) activity, lateral movement, data exfiltration, and ultimately data encryption and the writing of ransom notes.
Darktrace’s AI understands customer networks and learns the expected patterns of behavior across an organization’s digital estate. Using its anomaly-based detection Darktrace is able to identify emerging threats through the detection of unusual or unexpected behavior, without relying on rules and signatures, or known IoCs.
Network Security Challenge 3: Spotting Novel Attacks
You can’t predict tomorrow’s weather by reading yesterday’s forecast, yet that’s essentially what happens when network security tools only look for known attacks.
What are novel attacks?
“Novel attacks” include unknown or previously unseen exploits such as zero-days, or new variations of known threats that evade existing detection rules.
Depending on how threats get executed, the term “novel” can refer to brand new tactics, techniques, and procedures (TTPs), or to subtle new twists on perennial threats like DoS, DDoS, and Domain Name Server (DNS) attacks.
Old tools may be blind to new threats
Stopping novel threats is less about deciding whom to trust than it is about learning to spot something brand new. As we’ve seen with ransomware, the growing “aaS” attack market creates a profound paradigm shift by allowing non-technical perpetrators to tweak, customize, and coin never-before-seen threats that elude traditional network, email, VPN, and cloud security.
Tools based on traditional rules and signatures lack a frame of reference. This is where AI’s ability to spot and analyze abnormalities in the context of normal patterns of life comes into play.
Darktrace AI spots what other tools miss
Instead of training in cloud data lakes that pool data from unrelated attacks worldwide, Darktrace AI learns about your unique environment from your environment. By flagging and analyzing everything unusual — instead of only known signs of compromise — Darktrace’s Self-Learning AI keeps security stacks from missing less obvious but potentially more dangerous events.
The real challenge here is achieving faster “time to meaning” and contextualizing behavior that might — or might not — be part of a novel attack. Darktrace/Network does not require a “patient zero” to identify a novel attack, or one exploiting a zero-day vulnerability.
Use Case: Stopping Novel Ransomware Attack
In late May 2023, Darktrace observed multiple instances of Akira ransomware affecting networks across its customer base. Thanks to its anomaly-based approach to threat detection Darktrace successfully identified the novel ransomware attacks and provided full visibility over the cyber kill chain, from the initial compromise to the eventual file encryptions and ransom notes. Darktrace identified Akira ransomware on multiple customer networks, even when threat actors were utilizing seemingly legitimate services (or spoofed versions of them) to carry out malicious activity. While this may have gone unnoticed by traditional security tools, Darktrace’s anomaly-based detection enabled it to recognize malicious activity for what it was. In cases where Darktrace’s autonomous response was enabled these attacks were mitigated in their early stages, thus minimizing any disruption or damage to customer networks.
References
[1] Gartner, “Gartner Unveils Top Eight Cybersecurity Predictions for 2023-2024,” 28 March 2023.
[2] TechTarget, “Ransomware trends, statistics and facts in 2023,” Sean Michael Kerner, 26 January 2023.